H.R. 7121: Securing Federal Devices from Chinese Applications Act
This bill, known as the "Securing Federal Devices from Chinese Applications Act," aims to prevent the download or use of applications developed or controlled by Chinese entities on federal government devices. Its main provisions include:
Prohibition on Chinese Applications
The bill states that federal agencies are prohibited from downloading or using certain applications, termed "covered applications," on their devices. The only exception is if the head of a federal agency determines that the use of such an application is necessary for research or intelligence purposes required by law.
Definition of Covered Applications
Covered applications are defined as applications that:
- Are developed, owned, or controlled by entities headquartered in China;
- Are controlled by entities in which the Chinese government or Communist Party holds a controlling interest;
- Are determined by the Secretary of Defense to pose a risk to U.S. national security.
Guidelines for Exceptions
Within 270 days of the bill's enactment, agency heads are required to issue guidelines regarding any exceptions to the prohibition. These guidelines must ensure cybersecurity safeguards and include requirements to document risk mitigation actions.
Creation and Update of Covered Application List
The Director of the Office of Management and Budget, in consultation with other federal security officials, is tasked with creating and periodically updating the list of covered applications. This list must be updated every 180 days.
Removal of Covered Applications
Once an application is identified as a covered application, the head of each agency must ensure its removal from federal devices within 60 days.
Definitions Relevant to the Bill
- Agency: Refers to any executive department, military department, government corporation, or independent regulatory agency within the federal government. Local governments and territories are not included.
- Cybersecurity: Defined broadly as the measures in place to prevent damage to, unauthorized access to, and exploitation of electronic information systems, along with restoration efforts as necessary to maintain system integrity.
Implementation Timeline
The bill includes specific timelines for actions to be taken, such as the guidelines for exceptions (270 days post-enactment), the creation of the covered application list (180 days post-enactment), and the removal deadline for identified applications (60 days post-identification).
Relevant Companies
- TCEHY (Tencent Holdings Ltd.): This company could be impacted as it controls multiple applications that may fall under the definition of covered applications.
- BABA (Alibaba Group Holding Limited): Similar to Tencent, Alibaba develops and owns various applications that may be banned under this bill.
- 0700 (Tencent): Specific applications owned by Tencent could also be scrutinized under the terms of this legislation.
This is an AI-generated summary of the bill text. There may be mistakes.
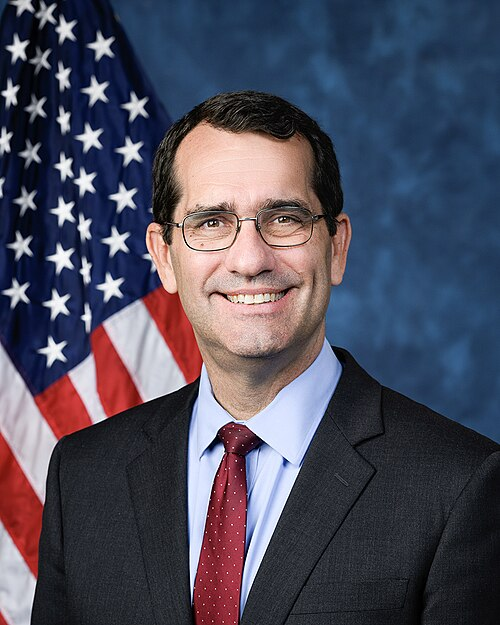
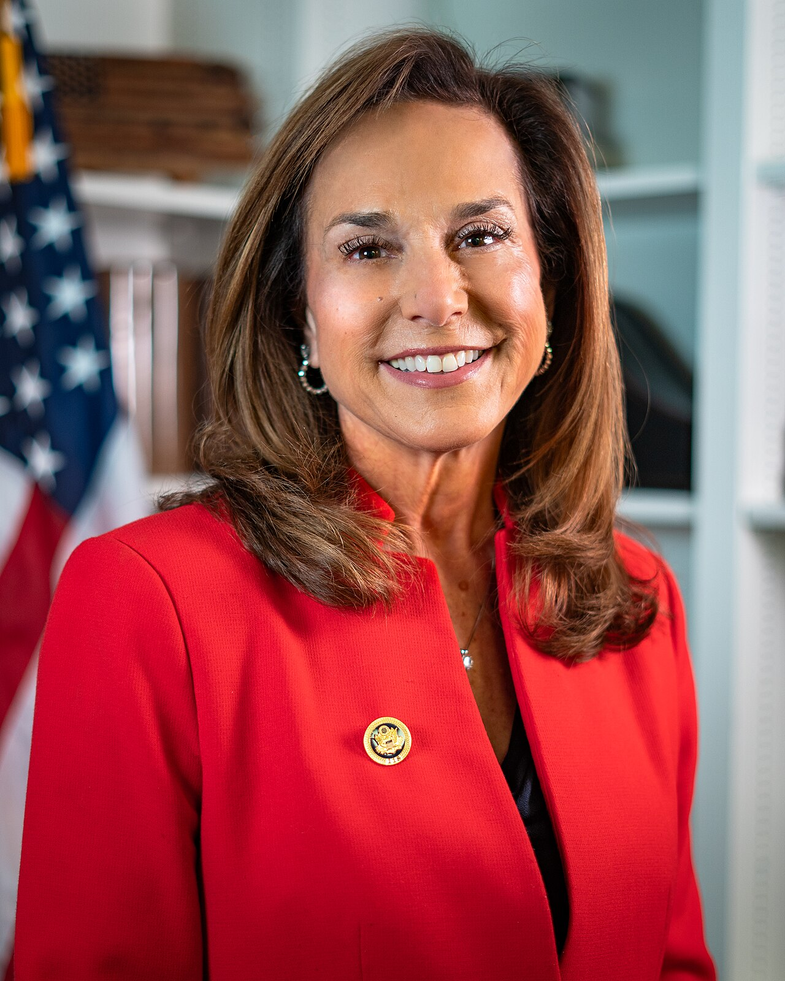
Sponsors
4 bill sponsors
Actions
2 actions
| Date | Action |
|---|---|
| Jan. 15, 2026 | Introduced in House |
| Jan. 15, 2026 | Referred to the House Committee on Oversight and Government Reform. |
Corporate Lobbying
0 companies lobbying
None found.
* Note that there can be significant delays in lobbying disclosures, and our data may be incomplete.